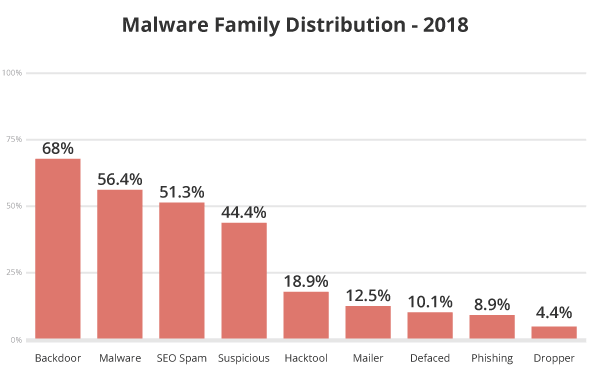
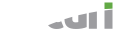
Our 2018 research included infection trend analysis and how it correlates to malware families.
Malware families allow our team to assess an attacker’s tactics, techniques, and procedures (TTP). This information inevitably leads us to their intentions and helps us understand and mitigate future threats.
Note:
- The suspicious category includes all signatures that could not be classified in a known family.
- A hacked website may have multiple files modified with different malware families, which explains why totals exceed 100%.
In 2018, 68% of all cleanup requests revealed at least one PHP-based backdoor hidden within the site; this percentage dropped 3% from 2017. A drop of 3% does not negate the relevance or importance of doing deep scans. It is still the No.1 leading infection out of all cleanup requests analyzed by the team.
Backdoors function as the point of entry into a website’s environment after a successful compromise and are one of the first things an attacker will deploy to ensure continued access. These tools allow an attacker to retain unauthorized access to an environment long after they have successfully infected a website.
In many instances, we see attackers scanning sites for known backdoors in target hosts, looking to potentially abuse another attacker’s backdoor. Backdoors give attackers the opportunity to bypass existing access controls to web server environments and are particularly effective at eluding modern website scanning technologies. This makes them one of the most commonly missed payloads and a leading cause of reinfections.
The primary intent is within the attack itself — found in the form of malicious redirects, SEO spam, drive-by-download infections, and other forms of malware.
We discovered a sharp increase in the general malware family distribution – from 47% in 2017 to 56.4% in 2018. Attacks within this category are primarily related to the usage of PHP functions with undetermined payloads that don’t meet the criteria for other families.
Mailer script infections decreased from 19% to 12.50%. Mailers abuse server resources and allow bad actors to send unwanted emails from a domain. These forms of malware can wreak havoc by distributing malware or phishing campaigns and stealing sensitive information.
51.3% of all infection cases in 2018 were related to SEO spam campaigns; up 7.3% from the previous year. This is one of the fastest growing families over the previous years. They are difficult to detect and have a strong economic engine driven by impression-based affiliate marketing. Most frequently, the result of Search Engine Poisoning (SEP) attacks, where attackers attempt to abuse site rankings to monetize on affiliate marketing or other blackhat tactics, SEO spam typically occurs via PHP, database injections, or .htaccess redirects.
Websites impacted by SEO attacks often become infected with spam content or redirect visitors to spam-specific pages. Unwanted content is regularly found in the form of pharmaceutical ad placements but may also include injected content for other popular industries like fashion or entertainment (i.e. pornographic material, essay writing, fashion brands, loans, and online gambling).
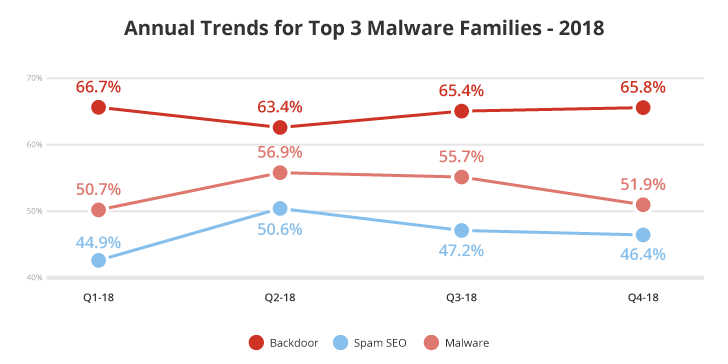
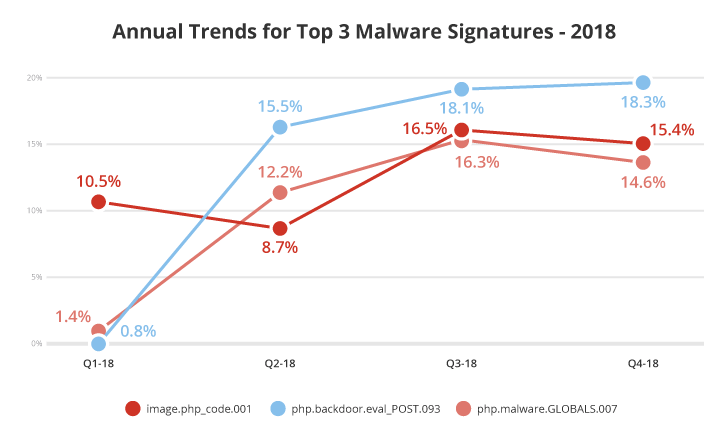
According to the annual trends shown above for the top three threats, we see an overall downward trend for Malware and SEO spam after Q2-2018.
In general, the Malware family represents a more generic family of attacks including payment information stealers, malicious trackers and ad networks, injections from paste sites and URL shorteners, cryptominers, and exploits. The SEO Spam family is comprised of attacks that specifically target the manipulation of search engine optimization.
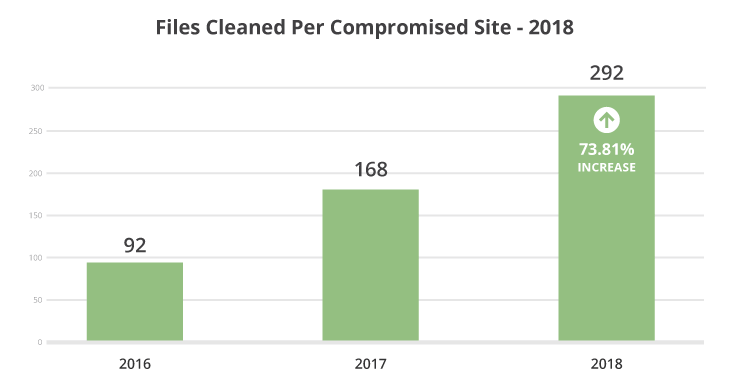
We cleaned approximately 292 files during each malware removal request, a 73.81% increase from 2017.
This data indicates an increase in the depth of files being affected during a website compromise. It also demonstrates why cleaning the symptom from one file is often not enough to completely remove an infection.
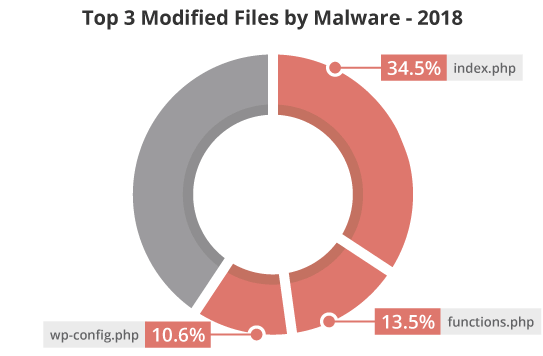
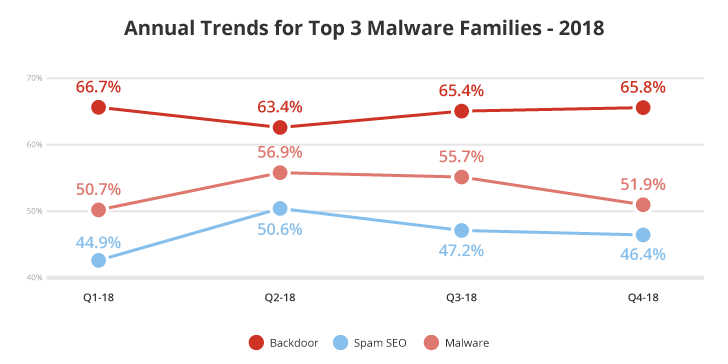
Our analysis also identified the top files modified after a successful compromise.
34.5% of sites had their index.php files modified after a compromise, indicating that this file is an important asset that should be included in file integrity monitoring systems. Index files are found on nearly every PHP site and are guaranteed to be loaded during web page generation. This makes them prime infection targets for bad actors. These files are modified by attackers for a variety of reasons including malware distribution, server scripts, phishing attacks, blackhat SEO, conditional redirects, and defacements.
We also identified that 13.5% of sites had modified functions.php files after a successful attack. These files are often used to deploy SEO spam and other malicious payloads, including backdoors and injections.
The third most common file modified after a compromise was wp-config.php (10.6%), a reflection of the number of cleanup requests seen for WordPress sites in the past year. This file contains sensitive information about the database, including name, host, username, and password. It is also used to define advanced settings, security keys, and developer options.
There are a number of reasons why the index.php, functions.php and wp-config.php files make for popular targets among attackers:
- They are loaded on every site access.
- They belong to a group of core files not overwritten during WordPress updates.
- They are often ignored by integrity monitoring systems, as the value often changes frequently.
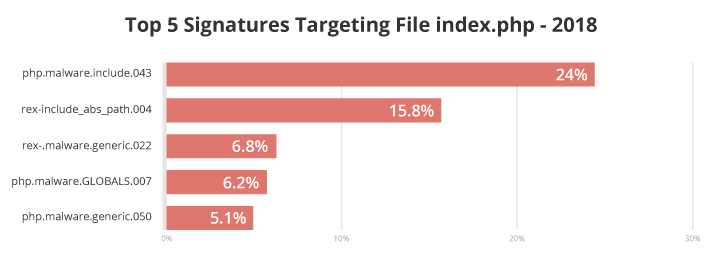
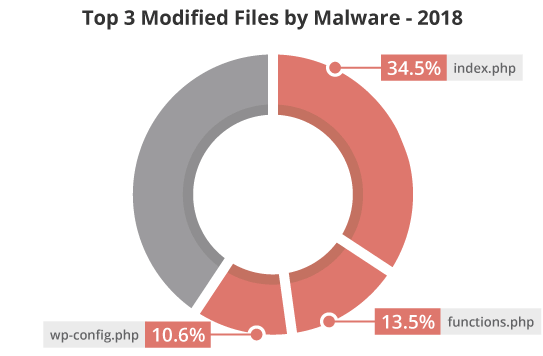
During our analysis, our researchers identified that the following signatures were most commonly associated with these modified files:
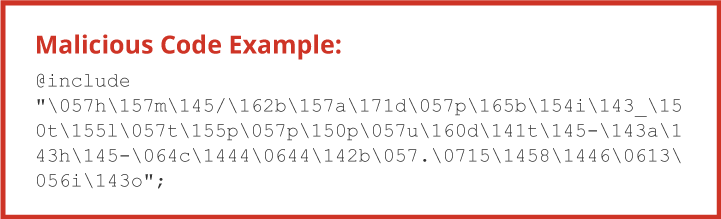
Twenty-four percent of index.php files were associated with the malware signature php.malware.include.043. This signature detects an obfuscation method responsible for hiding a file inclusion (calls to PHP functions like include and include_once) by replacing the file path characters with their correspondence in Hexadecimal and mixing up with alphabetic characters – example below.
The second most common malware signature for index.php (15.8%) was rex.include_abs_path.004. This signature looks for files called by PHP scripts using absolute paths and obfuscated characters within seemingly innocent files.
The remaining top malware signatures associated with index.php are for generic malware signatures and PHP malware.
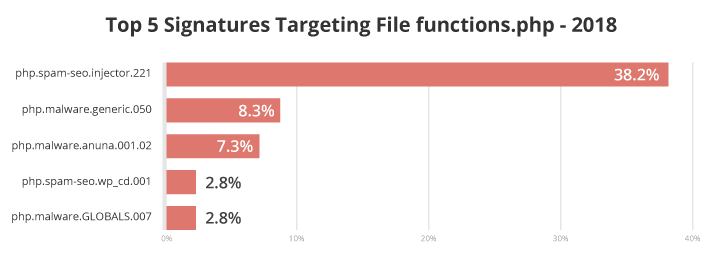
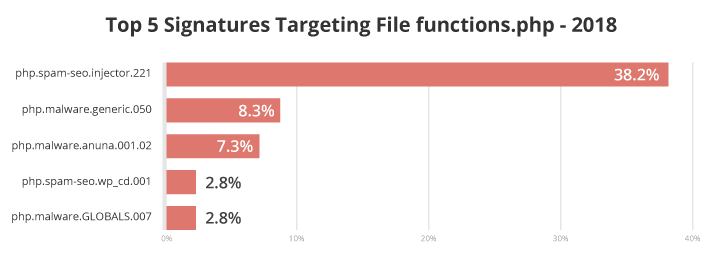
Over 38% of functions.php files were associated with the malware signature php.spam-seo.injector.221. This signature detects malware that loads random content from a third-party URL and injects it on the affected site. One of its most interesting functions is the ability to update the configurations through a remote command. It doesn’t explicitly act as a backdoor, but it can use the function to load any kind of code – including a backdoor. We usually find it on nulled or pirated themes and plugins
The second most common malware signature associated with functions.php files was php.malware.generic.050, impacting 8.3% of files. This is one of our favorite heuristic signatures that relies on multiple triggers to clear a malicious eval call.
7.3% of functions.php files were associated with the malware signature php.malware.anuna.001.02. Named after the condition commonly required to run malicious content, the malicious payloads vary from spam injection, backdoors, creation of rogue admin users, and a variety of other objectionable activities.
The signature php.spam-seo.wp_cd.001 (2.8%) is related to malware that loads injected content and can be found on nulled themes. Signature php.malware.GLOBALS.007 (2.8%) is generic and relies on a number of different triggers to identify the malicious usage of PHP GLOBALS variables.

Also commonly seen with index.php files as described above, 11.3% of wp-config.php files were associated with the malware signature php.malware.include.043.
9.1% of wp-config.php files were associated with the malware signature rex.include_abs_path.004. This signature looks for files called by PHP scripts using absolute paths and obfuscated characters within seemingly innocent file types.
The fifth most common signature seen targeting wp-config.php was php.backdoor.uploader.096 (1.1%), which looks for backdoors that can download code from a remote origin and upload it as a file on a compromised server.
We also identified the top three malware signatures of 2018:
The malware signature image.php_code.001 looks for backdoors that have been hidden as an image extension or appended to an existing image and loaded from another different loader component.
Our Knowledge Base offers extensive details and information about specific malware signatures.